Information Security is preparing a necessary upgrade to weblogin idpz (production weblogin service) in early 2021. We have done the early pilot testing of the new IdP software in December 2020 and the result is very positive. Our next step is a broader user acceptance testing in the community between Jan 5th and Feb 19th. This is a necessary step before we make the upgrade in the production.
User Acceptance Testing Instructions:
Prerequisite to Participate: participants need to be added to a private VPN grouper group. If you are not a Shibboleth SP administrator, please send an email with subject “Shibboleth IdP Upgrade UAT” to shib.admin@utoronto.ca. Make sure you include your UTORid in the email. It is necessary for us to enroll you to the UAT environment (Note: Shibboleth Service Provider (SP) administrators have been added to the group and already fulfill this requirement. )
Step 1. Download and install Cisco AnyConnect VPN Client if you don’t have it on your computer.
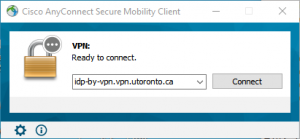
Step 2. Connect Cisco AnyConnect VPN to private VPN profile
- Enter idp-by-vpn.vpn.utoronto.ca in the Cisco AnyConnect Client and click “Connect” button.
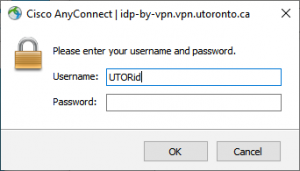
- Enter your UTORid and password in the pop-up window and click on “OK” button.
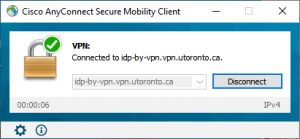
- If you the window below, then you have connected to the private VPN successfully.
Step 3. Log in to any applications protected by weblogin service (ex. Acorn, Quercus).
Step 4. Record the applications with failed login, then send the result back to shib.admin@utoronto.ca before Feb 19th.
Alternative Testing Instructions for Applications Requiring AdminsysVPN
If you need to test applications protected by AdminsysVPN, you can do a hosts file override before connecting to AdminsysVPN. You cannot connect to two Cisco VPN profiles at the same time.
Step 1: Open hosts file with administrator privilege
| Windows | MacOS/Linux Users |
|---|---|
|
|
Step 2: Add the following line in the file and save it.
128.100.132.207 idpz.utorauth.utoronto.ca
Step 3: Connect to AdminsysVPN and complete the UAT testing.
Step 4. Record the applications with failed login, then send the result back to shib.admin@utoronto.ca before Feb 19th.
